Send an Alert to Email
Send an Alert to Email
In this guide you'll learn how to enable Guardrails notifications and configure the notification rules to send email notifications. Similar configuration options exist to send notifications to Slack or Teams channels, and to generic webhooks. Our launch week announcement blog post includes a demo of notifications in action.
This is the eighth guide in the Getting started with Azure series.
Prerequisites
- Completion of the previous guides in this series.
- Access to the Guardrails console with administrative privileges.
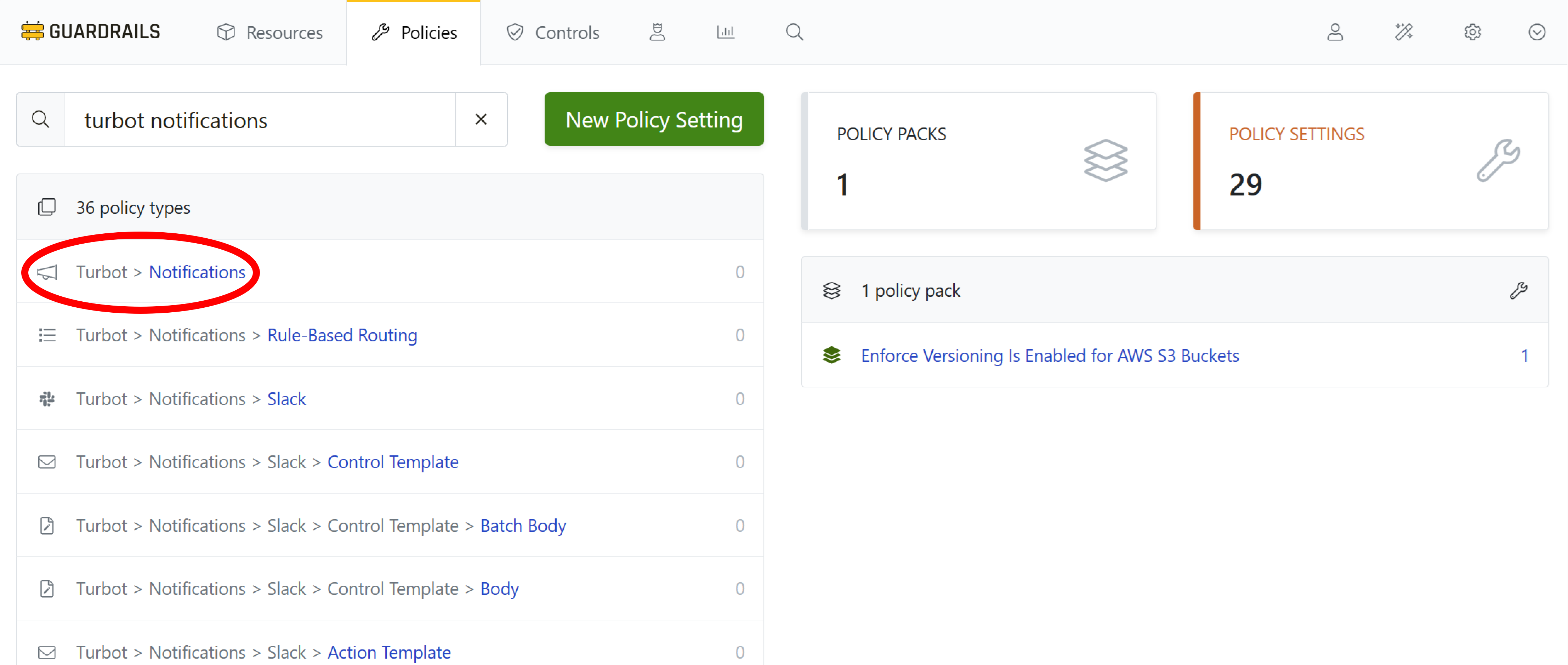
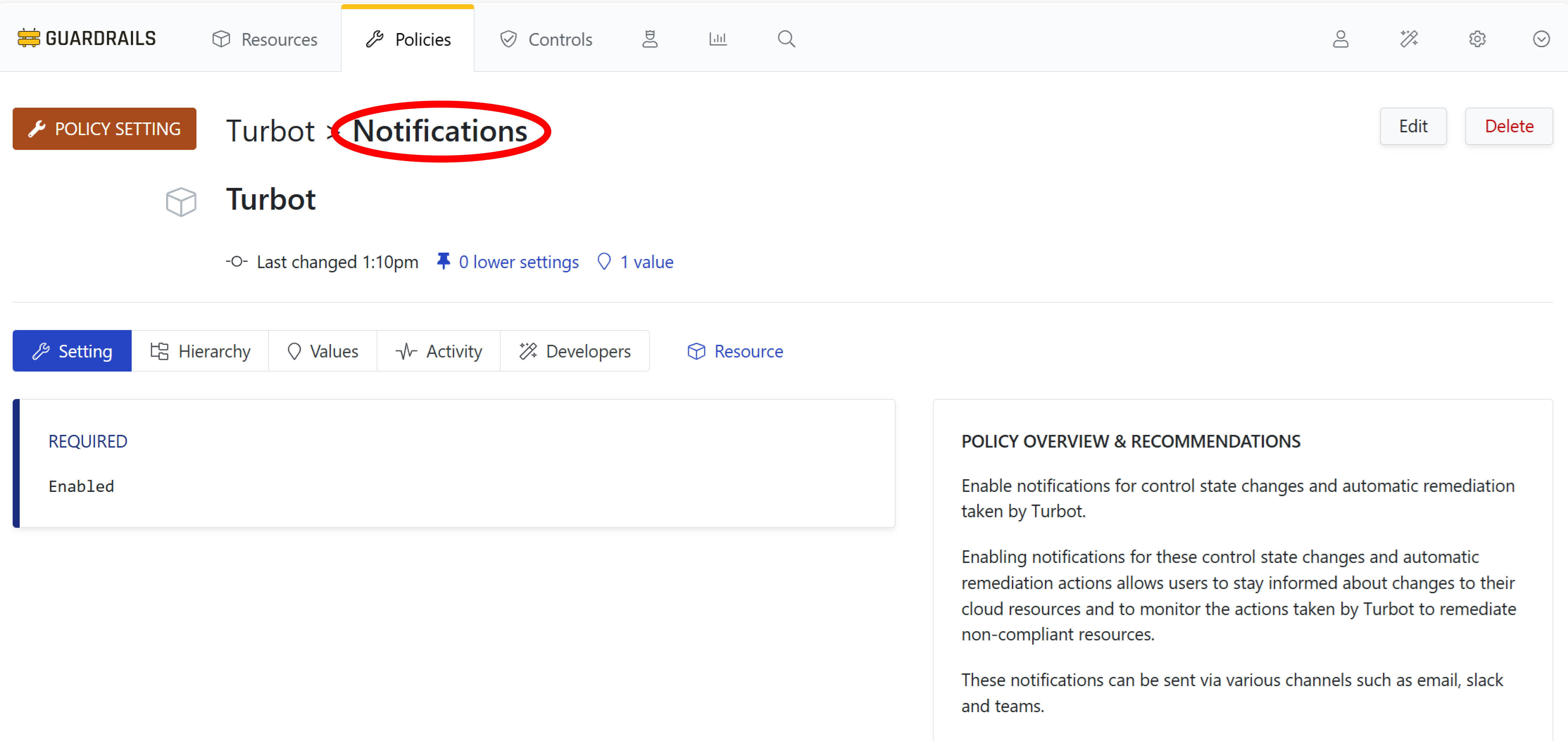
Step 1: Create policy setting
To enable notifications for your workspace, select Policies in the top navigation bar, and then search for turbot notifications. Select the Turbot > Notifications policy type.
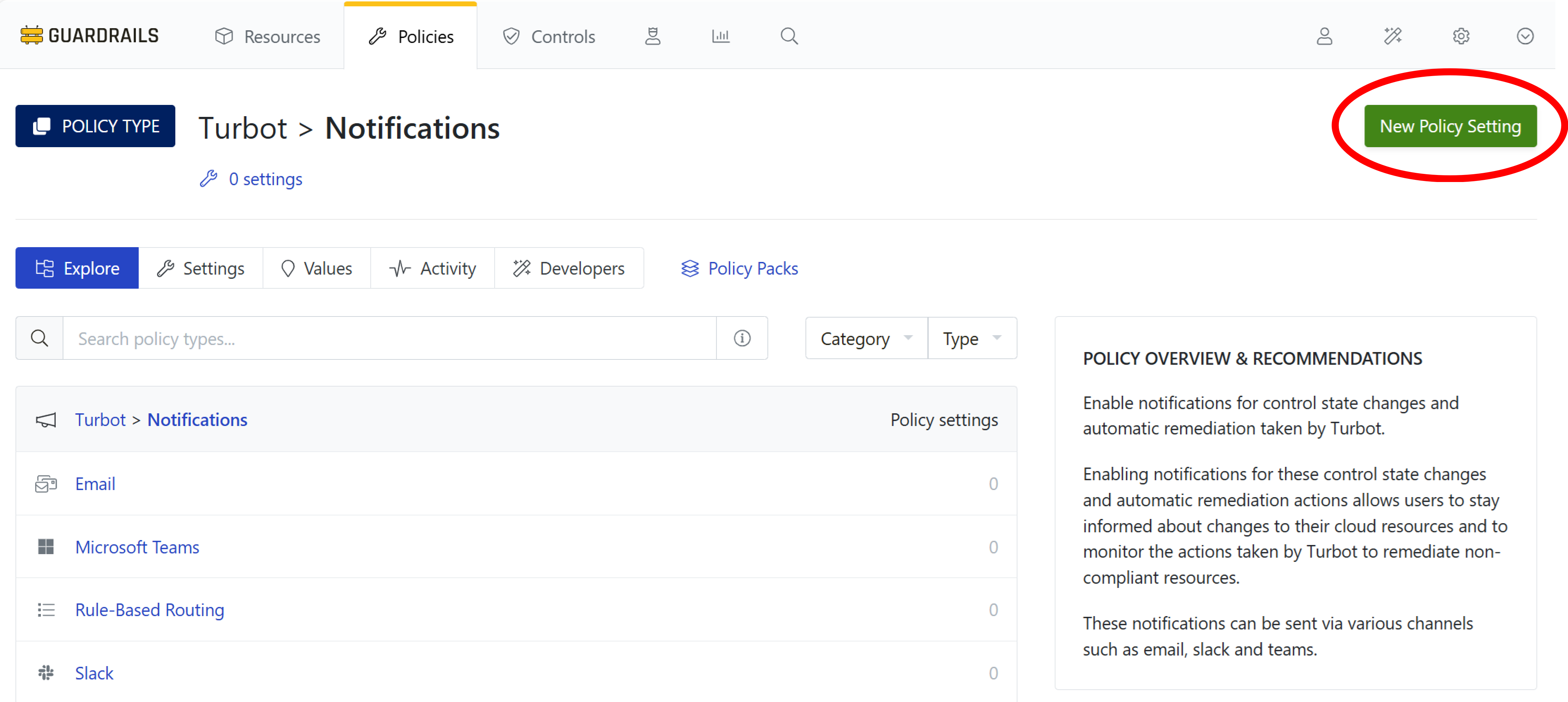
Select the New Policy Setting button.
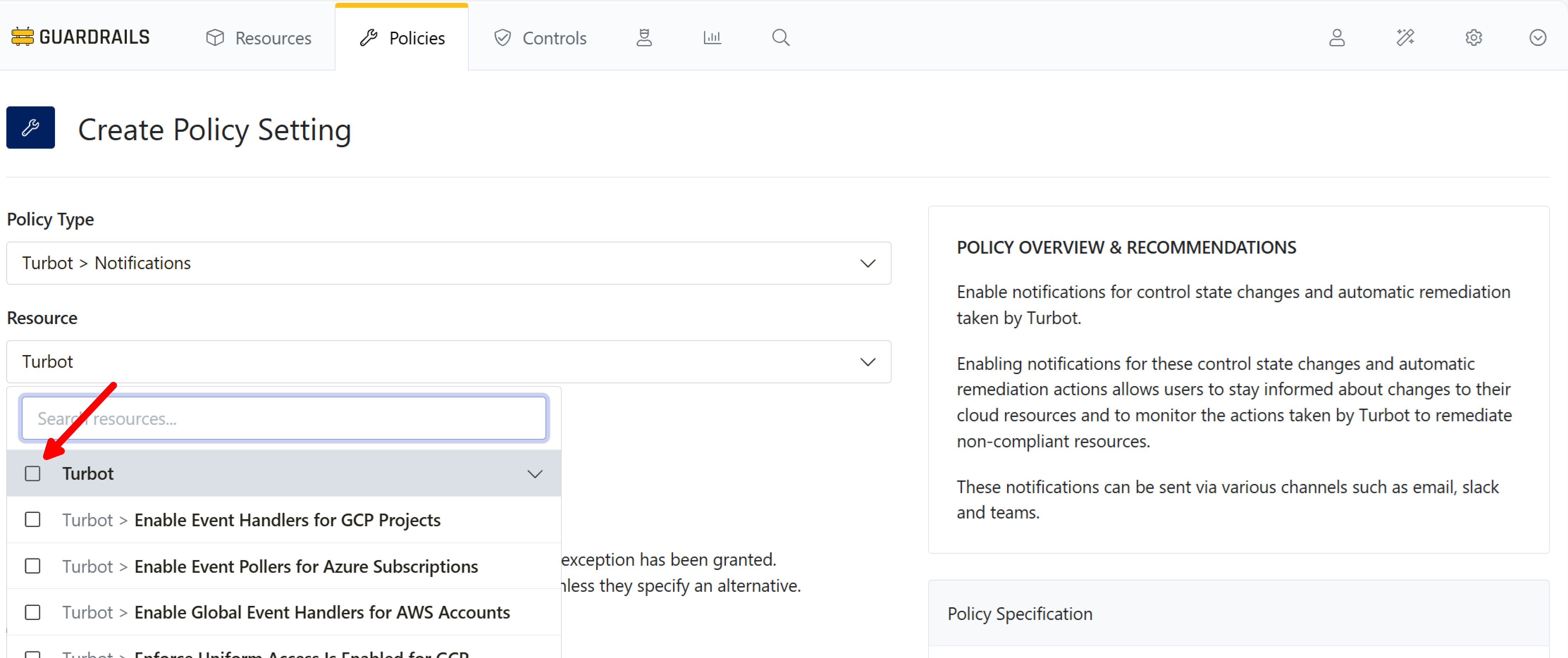
Step 2: Choose level
Select the Turbot root node as the resource.
[!NOTE] Notifications polices may only be created at the root level (aka Turbot level) of the resource hierarchy.
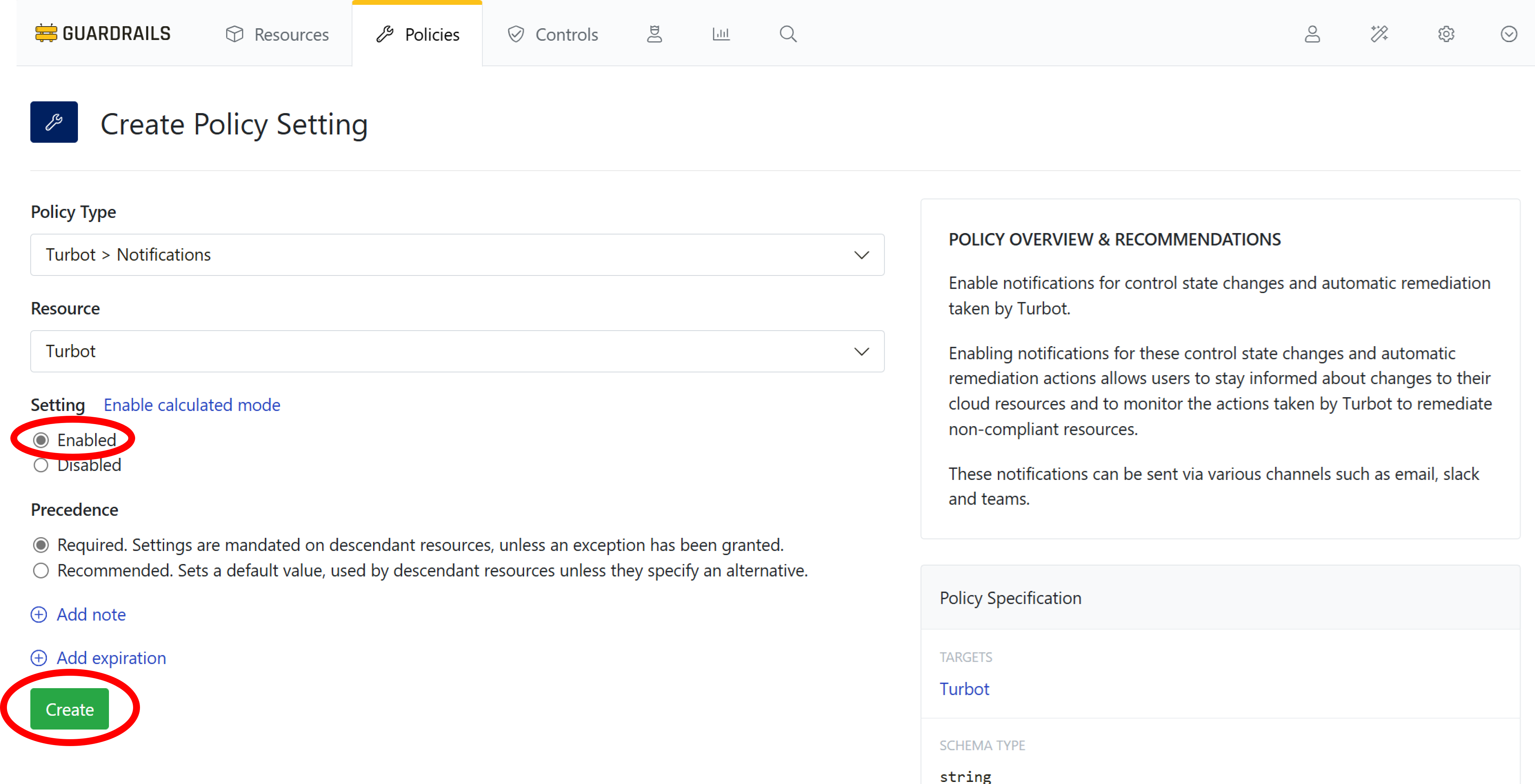
Step 3: Choose setting
Choose the Enabled setting. Then select Create.
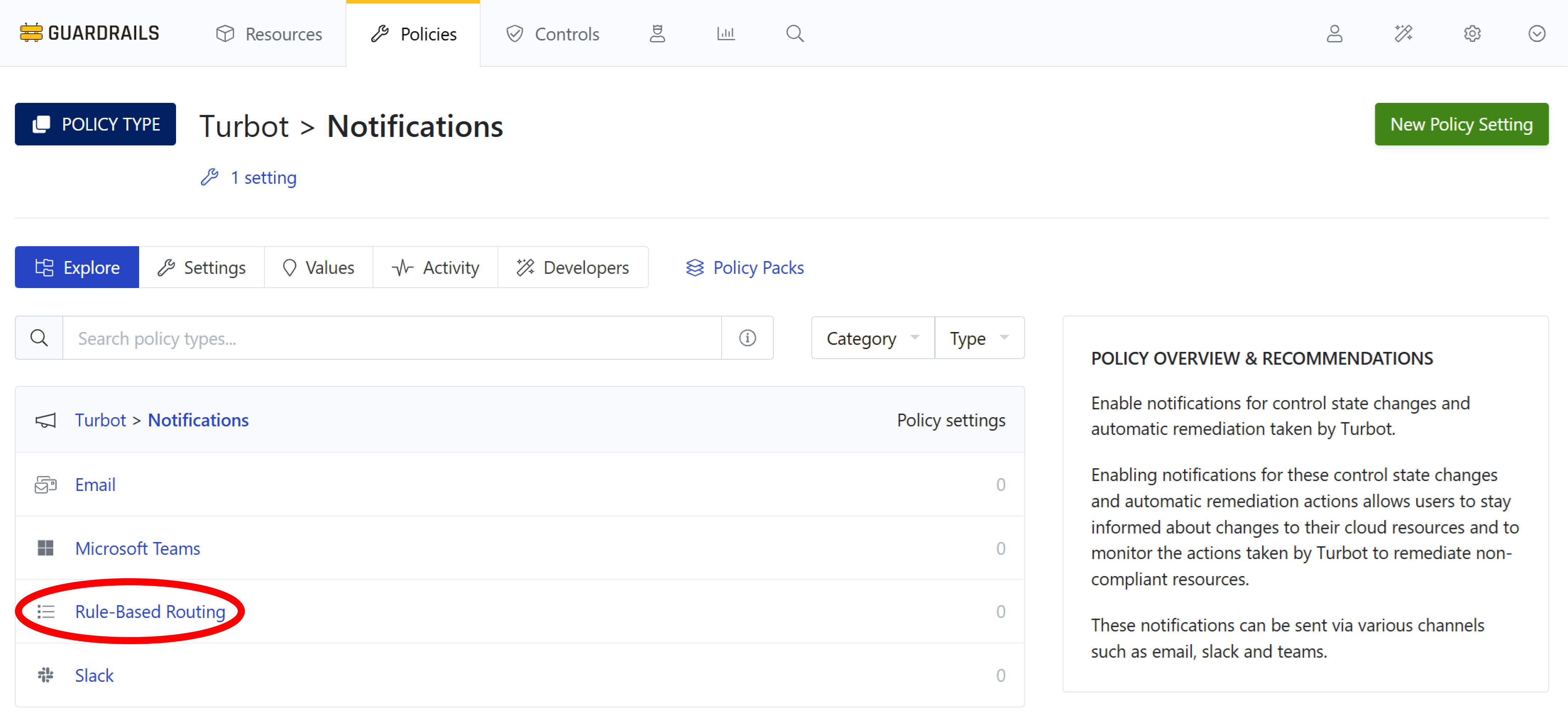
Step 4: List notifications policies
Navigate back to the list of Notification policies by clicking on the word Notifications in the Turbot > Notifications breadcrumb.
Step 5: Select Rules policy
Select the Rule-Based Routing policy type from the list of policies.
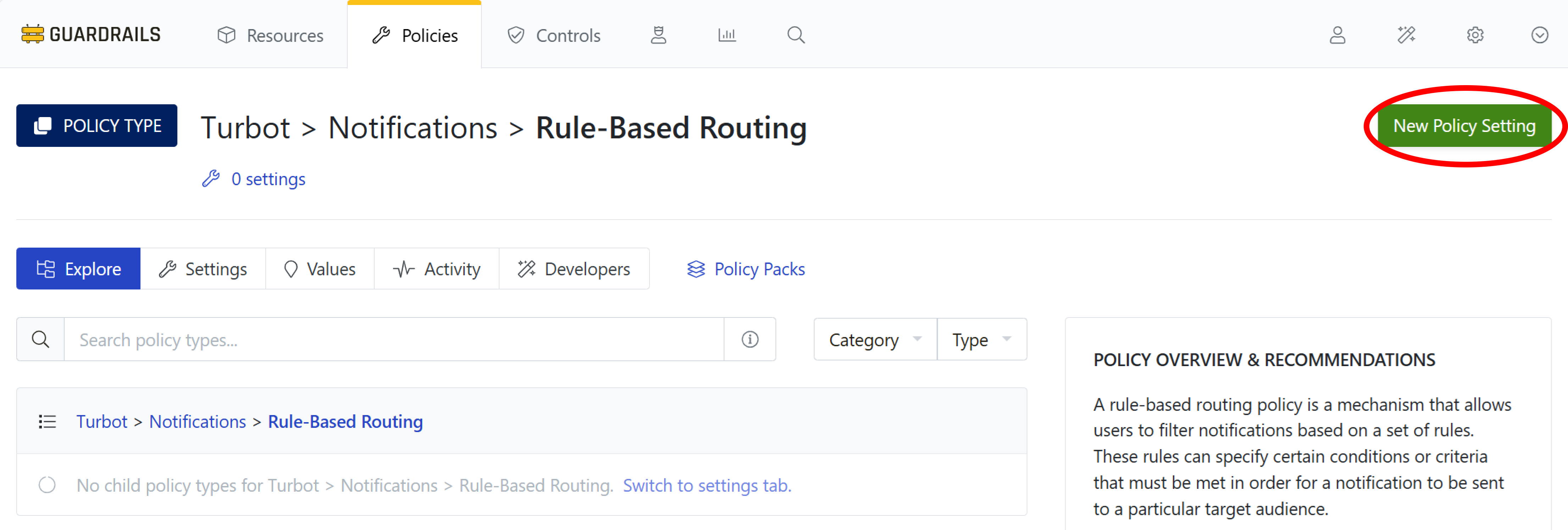
Step 6: View the Policy Type
Select New Policy Setting.
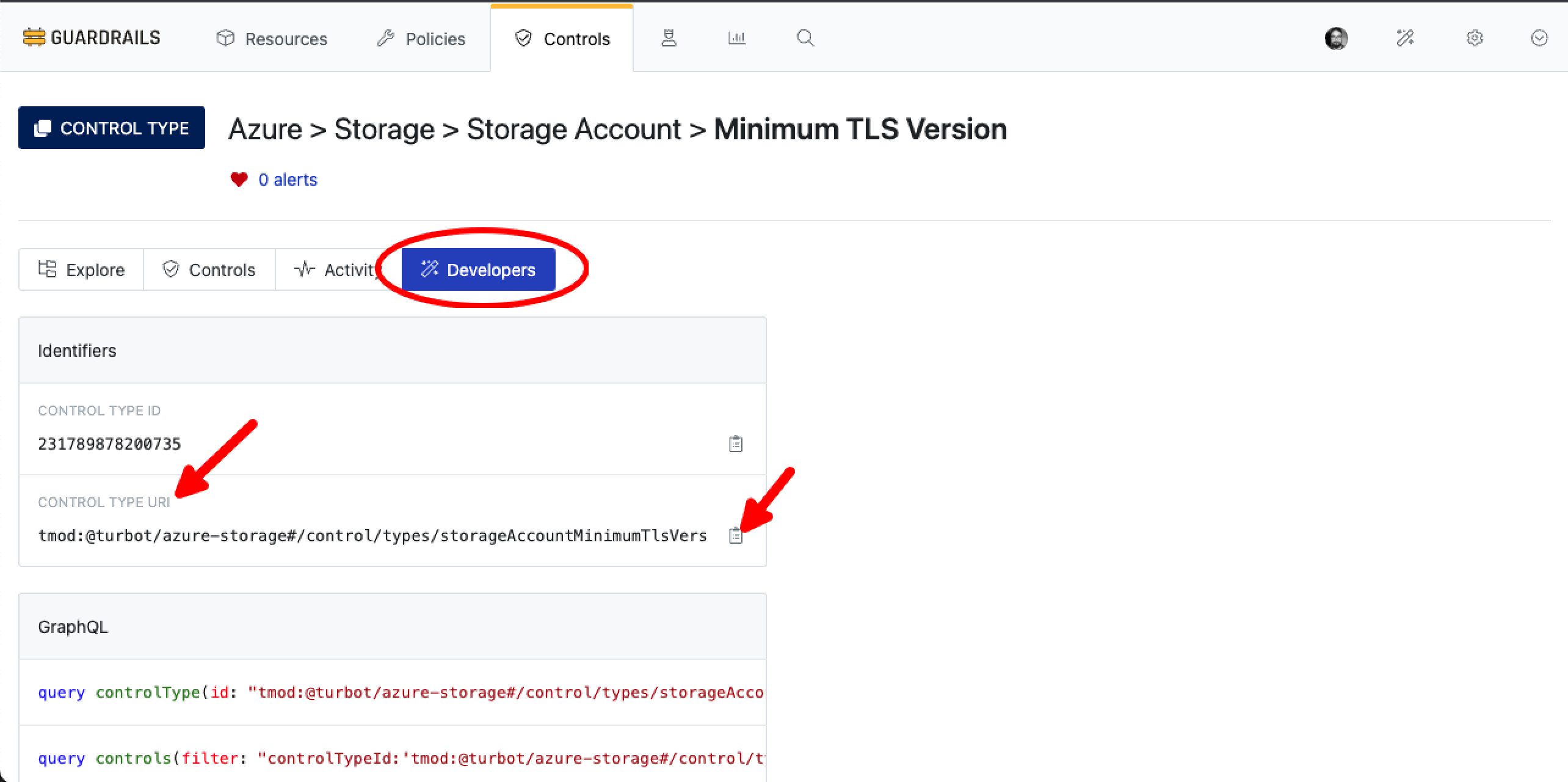
Step 7: Find control URI
Go top-level Controls, search for Azure > Storage > Storage Account > Minimum TLS Version, switch to the Developers tab, locate CONTROL TYPE URI and click to copy icon to copy the uri.
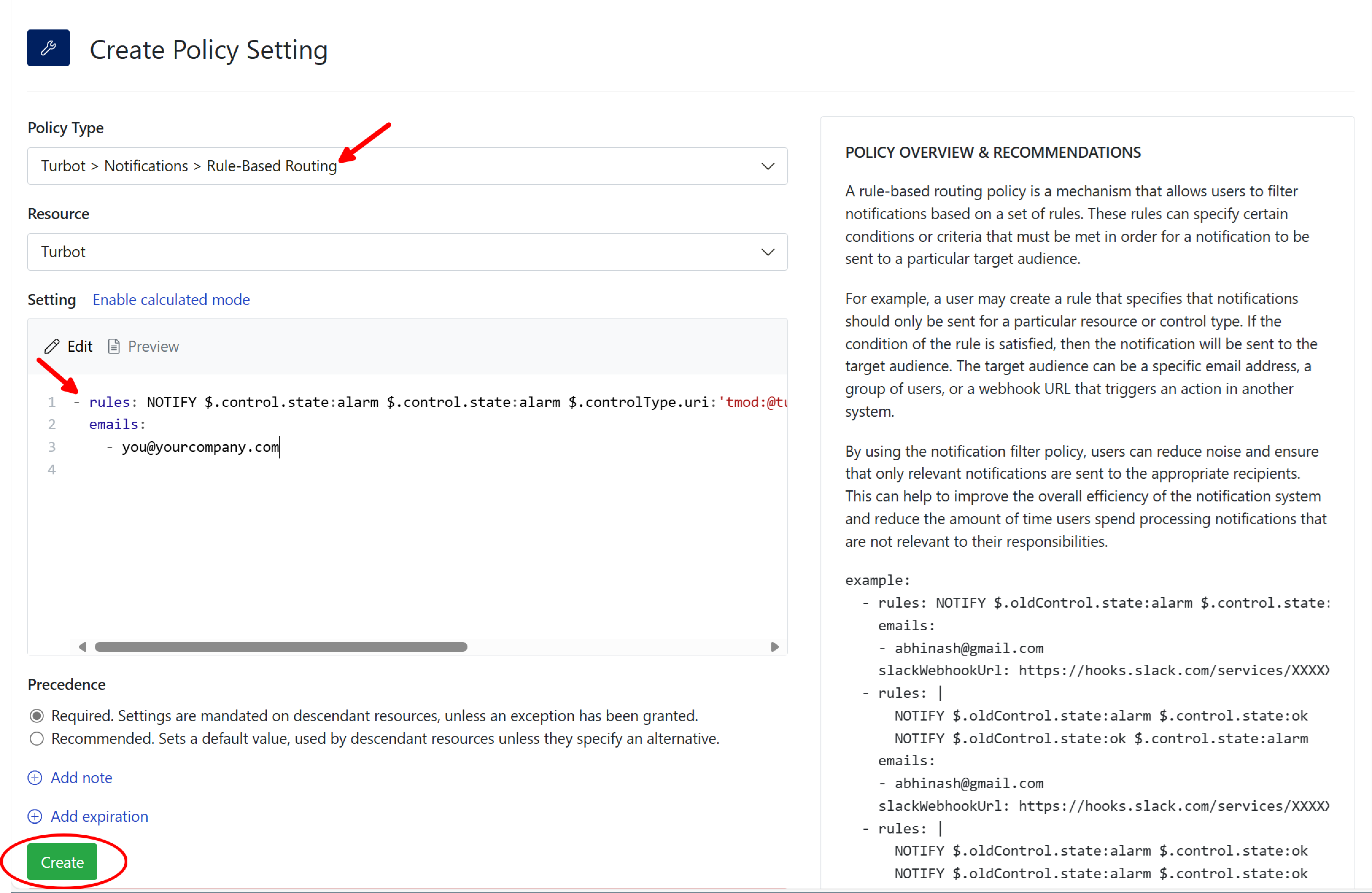
Step 8: Create notification rule
Again choose Turbot as the Resource. Copy and paste this rule, using one or more email addresses you want to notify. Specify the controlType uri as derived from Step:7
- rules: NOTIFY $.control.state:alarm $.control.state:alarm $.controlType.uri:'tmod:@turbot/azure-storage#/policy/types/storageAccountMinimumTlsVersion'
emails:
- [email protected]
The rule will send an alert to the configured email address when any control enters the Alarm state for storage account TLS version. See Notification Feature for more details.
Select Create.
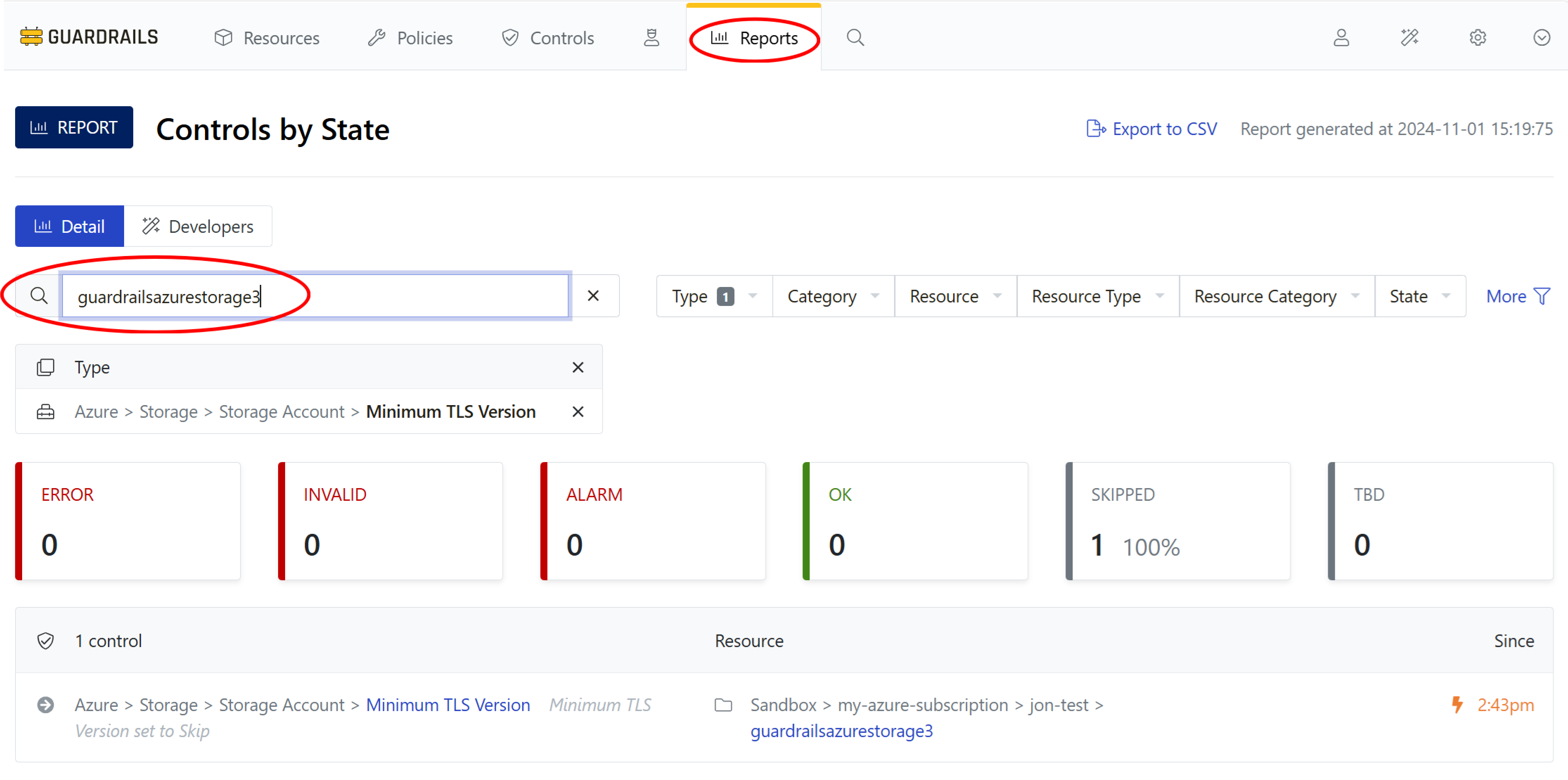
Step 9: Find the storage account skipped by your calculated policy
At the end of Create a calculated exception, your test storage account – the one you tagged with environment:development – was in a Skipped state for access control. To verify, revisit Controls by State in Reports menu, choose the Type as Azure > Storage > Storage Account > Minimum TLS Version, and search for the storage account.
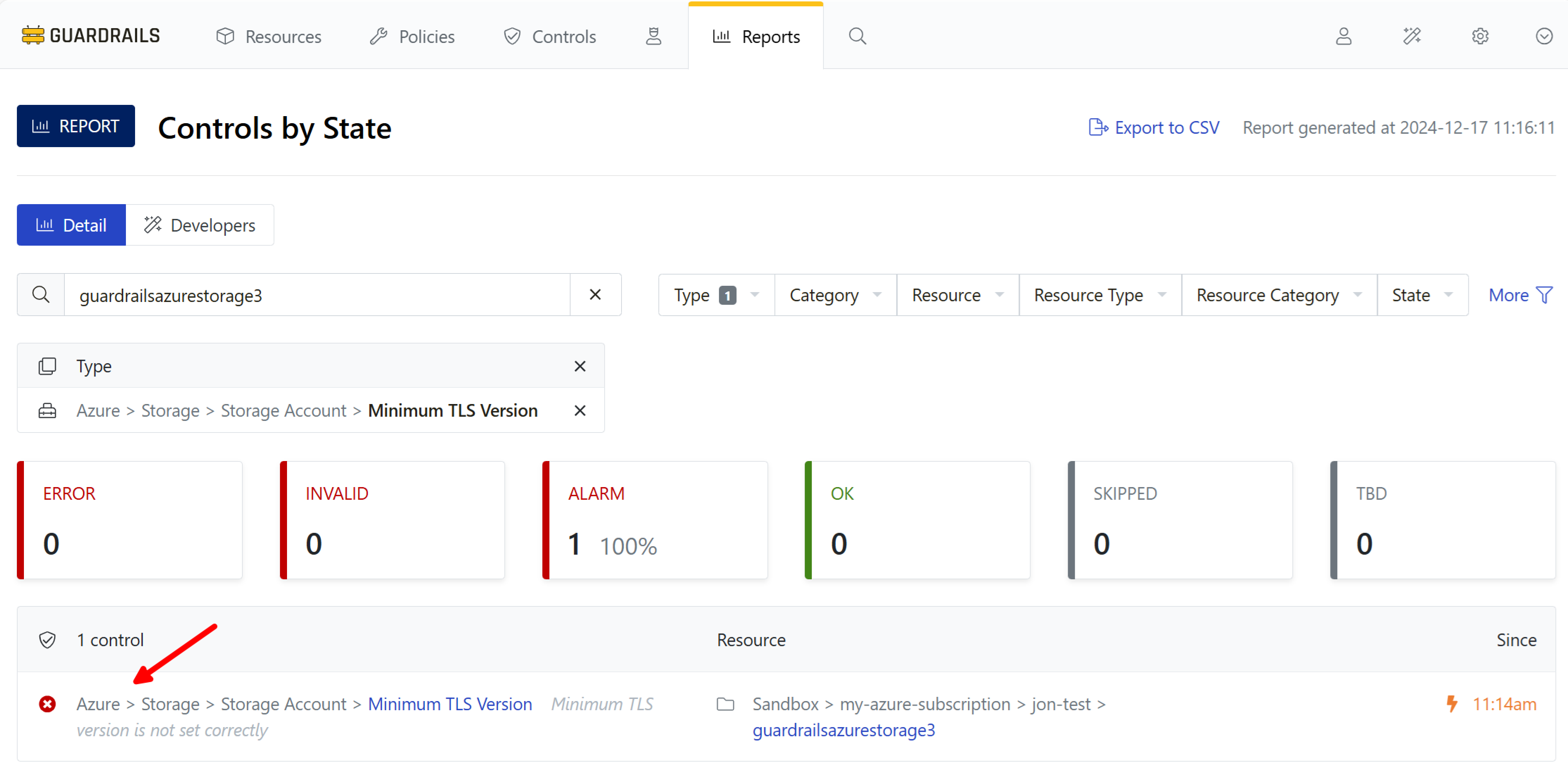
Step 10: Trigger the notification
Now, in the Azure portal console, change the tag environment:development to environment:production. The calculated policy setting, which had evaluated to Skip, now evaluates to Check: TLS 1.2. And because you left the setting at TLS 1.0, the control for that setting now transitions to Alarm.
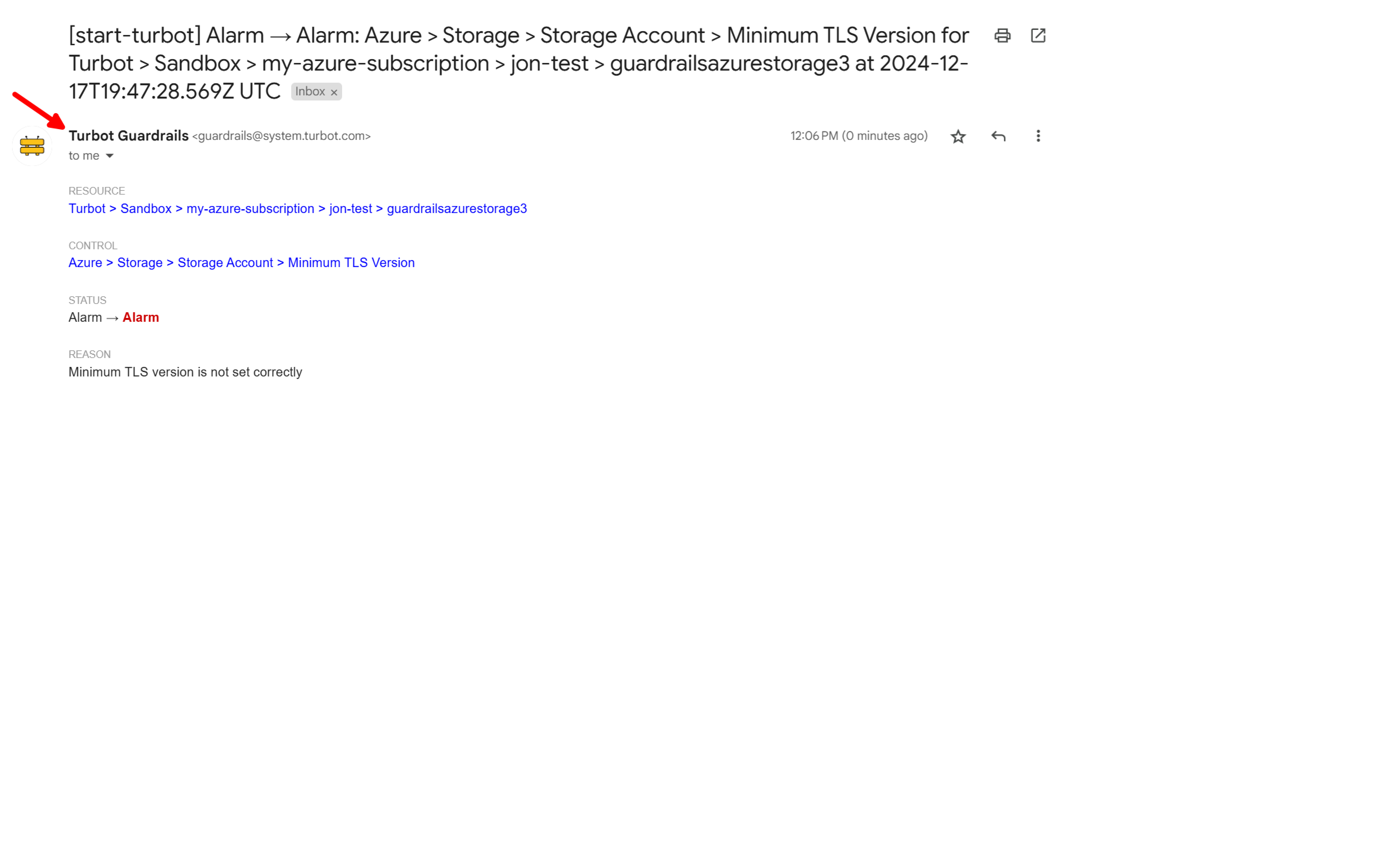
Step 11: Check your email
The alarm reported in the Guardrails console also appears in your inbox. You can alternatively configure Guardrails to send alerts to Slack or MS Teams.
Step 12: Review
In this guide you configured a simple notification rule and triggered a notification event.
Next Steps
In the next guide you’ll learn how to configure for Quick Actions so you can, for example, directly enforce TLS 1.2 on a storage account that’s now in the Alarm state and make it green.
Progress tracker
- Prepare an Azure Subscription for Import to Guardrails
- Connect an Azure Subscription to Guardrails
- Observe Azure Resource Activity
- Enable Your First Guardrails Policy Pack
- Review Subscription-Wide Governance
- Create a Static Exception to a Guardrails Azure Policy
- Create a Calculated Exception to a Guardrails Azure Policy
- Send an Alert to Email
- Apply a Quick Action
- Enable Automatic Enforcement