The cloud is moving at an unprecedented rate, with major cloud providers adding hundreds of new features a year. The rapid pace of innovation from providers like Amazon Web Services (AWS), Google Cloud Platform (GCP), Microsoft Azure, Oracle Cloud, and more requires enterprises to constantly adapt their governance practices to keep up with hundreds of services with millions of configuration permutations across their environments. The overall complexity of managing cloud at scale needs a new governance approach that is automated, provides real-time transparency, and self-healing intrinsic with your dynamic infrastructure.
Turbot Guardrails provides an out-of-the-box cloud governance framework that enables enterprises to mitigate security and operational risks. Turbot Guardrails cloud governance platform discovers all your resources, tracks changes in real-time and automatically organizes them into a CMDB with powerful search, visualization & reporting tools. Turbot Guardrails Policy Engine enables you to create rules for security, data protection, operations and cost controls with a single consistent, flexible and context-aware policy engine across all your clouds. In addition, Turbot Guardrails enables you to automate remediation and best practice setup of your cloud while letting your application teams use the tooling that makes them most productive. This provides a ready to use, enterprise grade, production ready platform to accelerate the maturity of your cloud governance and management.
Turbot Guardrails Controls are responsible for enforcing one or more policies. While Policies define the desired settings for Resources, Controls are responsible for implementing them. Turbot Guardrails Policies and Controls provide a flexible framework for auditing and enforcing configuration across hundreds of cloud services, networking, OS, and DB tiers. While this model is extensible, there are many guardrails that are common and consistent across AWS, Azure and GCP resources. This includes the CMDB and Discovery controls that inventory resources and populate the CMDB, the Approved Guardrails that enforce configuration standards when resources are created, the Active Guardrails that help clean up resources that are no longer used, as well as guardrails around encryption at rest, data protection, service enablement, and many others.
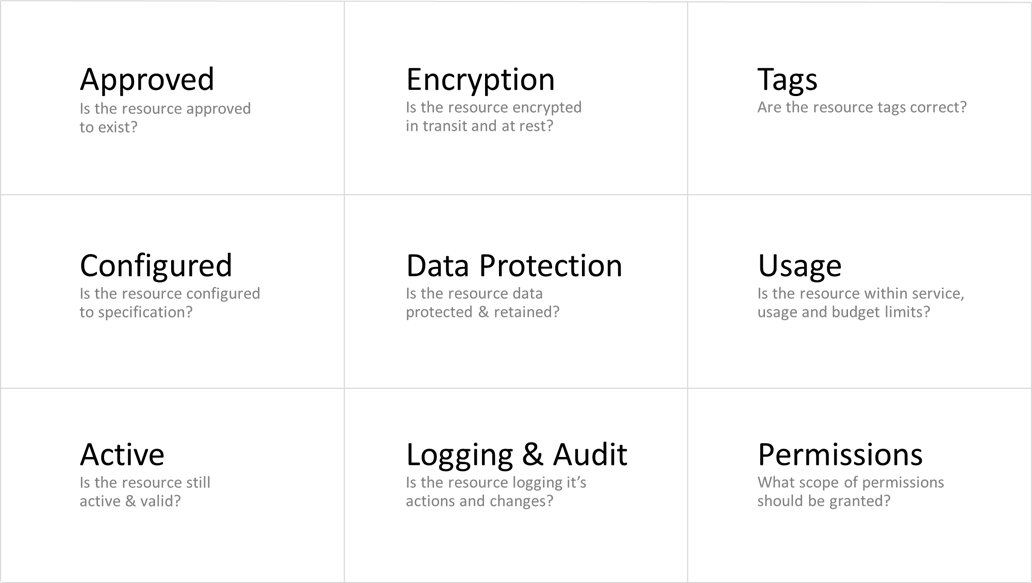
Examples of Turbot Guardrails Governance Control Categories. Control Categories provide an alternate, vendor agnostic, categorization of control types.
Controls are categorized into Control Categories as Control Types. A Control Type defines a specific control that may be configured for resources. For example, AWS > S3 > Bucket > Approved. A Control Type is associated with one or more policy types, which are context for the control. The Control Category Resource > Encryption at Rest includes many Encryption at Rest style controls such as AWS > S3 > Bucket > Encryption at Rest, GCP > Compute > Disk > Encryption at Rest, Azure > Storage > Storage Account > Encryption at Rest, etc.
Control Categories and Types are typically used for reporting, providing useful aggregation and filtering of data. Turbot Guardrails provides a fully graphed relationship between policies, controls, resources and activities to easily analyze control health per any organizational context.
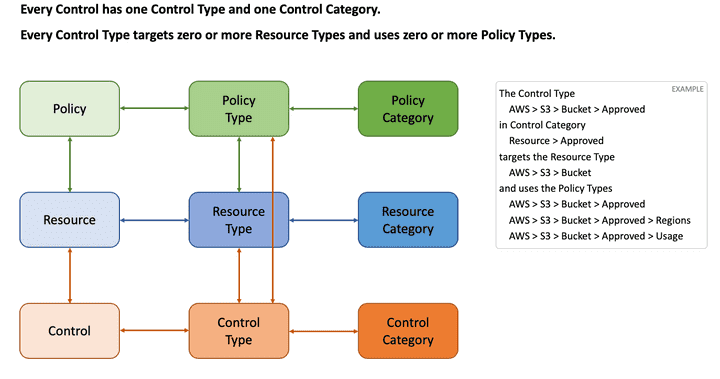
Conceptual diagram of Turbot Guardrails resource relationship relating Policies, Controls and Resources
As Turbot Guardrails discovers and remediates cloud configurations, Turbot Guardrails provides real-time control health reporting through Control States allowing you to watch, receive notifications, query, or report on how well your environment is adhering to your cloud governance framework.
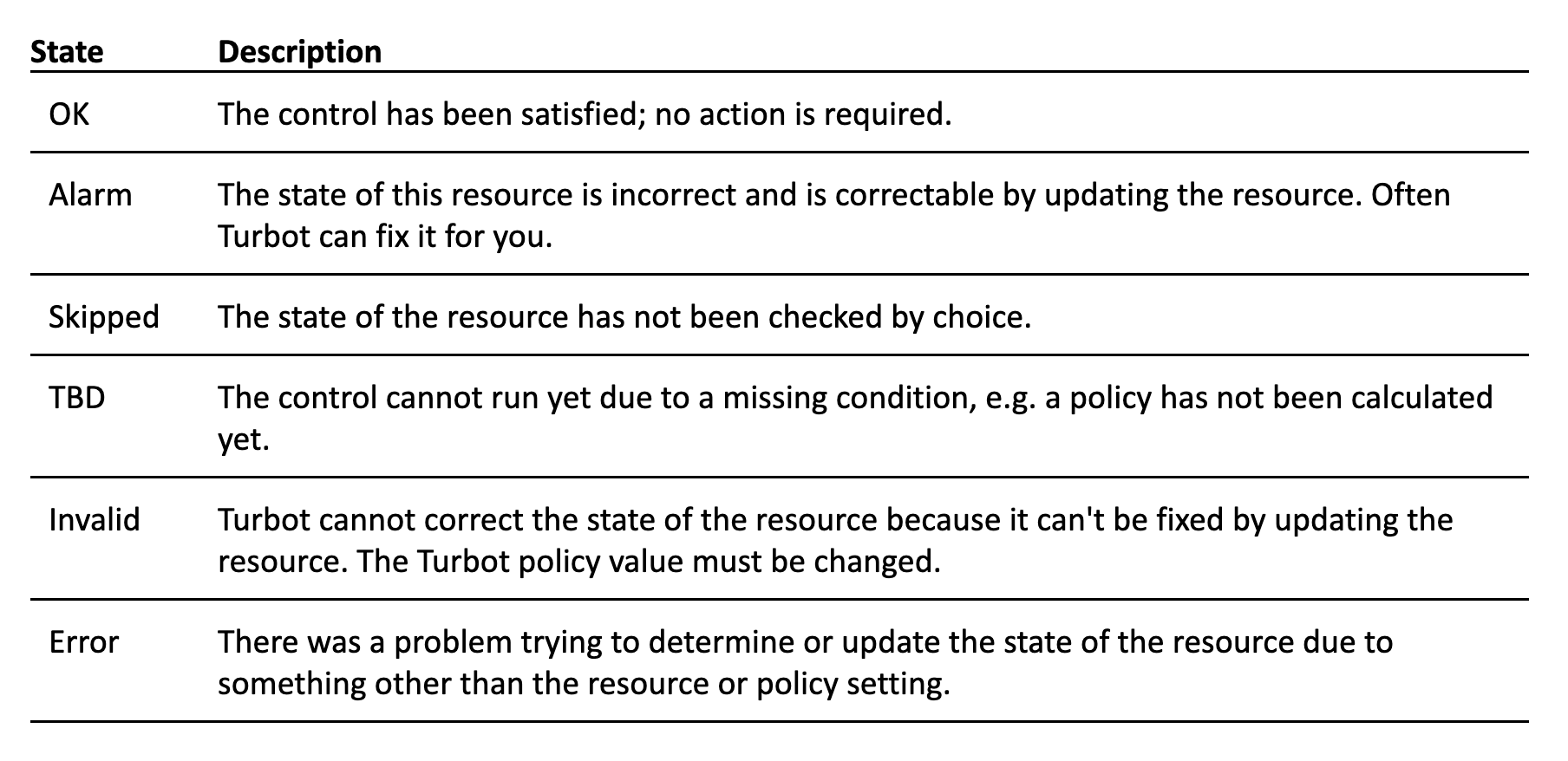
Turbot Guardrails Cloud Governance Reporting
As Turbot Guardrails discovers all your resources, tracks changes in real-time and automatically organizes them into our CMDB, Turbot Guardrails analyzes user changes and records all activity. As changes are analyzed, Turbot Guardrails own automated reasoning decisions, policy-based calculations, and actions are recorded through a rich time series of events which are all traceable.
As controls are changing, Turbot Guardrails provides an alarm-based history view of the control adherence which is accessible through the Turbot Guardrails Console and GraphQL API in real-time. Turbot Guardrails cloud governance reporting provides the ability to:
- Continuously monitor adherence to policies and controls
- Graph relationships of controls to resources and policies
- Capture detailed audit trail of configuration drift and user activity
- Search and visualize controls typed & categorized across your organizational hierarchy
- View detailed reporting dashboards through both the UI and API
Turbot Guardrails provides out-of-the-box capabilities of 1000s of defined Turbot Guardrails Governance Controls, as well as embedded 3rd party control frameworks such as Center for Internet Security (CIS), NIST 800-53, HIPAA, PCI, GDPR, etc. Customers can also customize Turbot Guardrails to visualize their own custom defined control frameworks built into the Turbot Guardrails platform.
Many of our enterprise customers are utilizing embedded control frameworks within Turbot Guardrails, particularly CIS Controls. Within Turbot Guardrails governance platform, users can visualize your cloud resources adherence to Center for Internet Security (CIS) Controls v6 and CIS Controls v7. Along with your adherence to the latest published CIS Amazon Web Services Foundations Benchmark, CIS Microsoft Azure Foundations Benchmark, CIS Google Cloud Platform Foundations Benchmark. Turbot Guardrails CIS dashboards are updated in real-time as changes occur in your cloud environment, providing instant visibility to how your organization is adhering to the well-established security best practices built into the CIS Benchmarks. When using Turbot Guardrails governance controls to remediate cloud security, compliance, operations and cost misconfigurations, Turbot Guardrails will continuously ensure adherence to CIS Controls and Benchmarks.
Curious how you can automate your company's adherence to CIS Controls or other industry best practices for security and compliance? Learn more about Turbot Guardrails Cloud Governance Controls in our whitepaper. You can also sign up for a free Turbot Guardrails Governance Control assessment. In a matter of minutes, visualize how your organization adheres to recognized best practices for securing IT systems and data against the most pervasive attacks.
