With the May 25th deadline for GDPR compliance rapidly approaching, Turbot Guardrails can support and enforce compliance for your public cloud. Many of our enterprise customers already use Turbot Guardrails guardrails to ensure continuous compliance of their cloud infrastructure with specific industry standards such as NIST 800-53 and CIS. Turbot Guardrails can help to enforce the specific standards documented in the GDPR regulations and can also support adherence to other security standards that can be leveraged to demonstrate GDPR compliance.
GDPR Article 32
Article 32 is the most applicable IT security component of the GDPR, which in itself only makes up about one page of extensive document. Turbot Guardrails can specifically help to accomplish these items from GDPR Article 32:
1(a): the [...] encryption of personal data
Turbot Guardrails can enforce encryption of data through automated guardrails.

1(b): the ability to ensure ongoing confidentiality, integrity, availability, and resilience of processing systems and services
Turbot Guardrails can be used to configure a combination of access control mechanisms, cryptographic mechanisms, and redundancy relevant to the confidentiality, integrity (to include alteration and destruction) and availability of data at-rest and in-transit. Turbot Guardrails offers continuous compliance through detective controls and real-time corrective actions by monitoring for events that would trigger non-compliance, and automatically applying the appropriate remediation.
To address cryptographic requirements, Turbot Guardrails can automate Encryption at Rest and Encryption in Transit configurations on many Cloud Services (e.g. AWS S3, AWS EBS Volumes, AWS Redshift, Azure Storage, Workspaces, etc.). And also, on the Linux tier, the Admins can block specific services (e.g. httpd, ftpd, etc.) allowed to run that may not support encryption in transit.
To address availability requirements, Turbot Guardrails itself is within a well-architected framework (immutable instances and microservices, highly available infrastructure). Turbot Guardrails has guardrails to allow / disable specific services to ensure only HA services are utilized. Turbot Guardrails also has guardrails to enforce High Availability architecture (e.g. VPC > NAT Gateway High Availability) and Networking patterns (e.g. VPC > Internet Route High Availability). Turbot Guardrails also has guardrails to ensure backups are created, retained, encrypted, rotated, and data loss prevention on accidental deletion across various services.
1(c): the ability to restore the availability and access to personal data in a timely manner in the event of a physical or technical incident
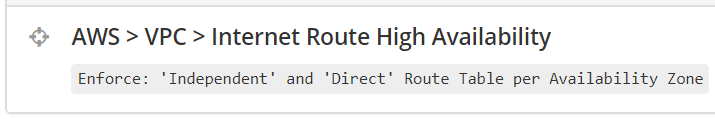
Turbot Guardrails has guardrails to allow / disable specific services to ensure only HA services are utilized. Turbot v also has guardrails to enforce High Availability architecture (e.g. VPC > NAT Gateway High Availability) and Networking patterns (e.g. VPC > Internet Route High Availability). Turbot Guardrails also has guardrails to ensure backups are created, retained, encrypted, rotated, and data loss prevention on accidental deletion across various services.
1(d): process for regularly testing, assessing and evaluating the effectiveness of technical and organizational measures for ensuring the security of the processing
Turbot Guardrails offers continuous compliance for its detective controls and real-time corrective actions by monitoring for events that would trigger non-compliance, and automatically applying the appropriate corrective action.
General GDPR Requirements
Turbot Guardrails can also be used to implement guardrails to enforce general topics required in GDPR:
For Data Sovereignty:
Turbot Guardrails has guardrails to ensure resources and data only reside in approved regions that our customers choose.
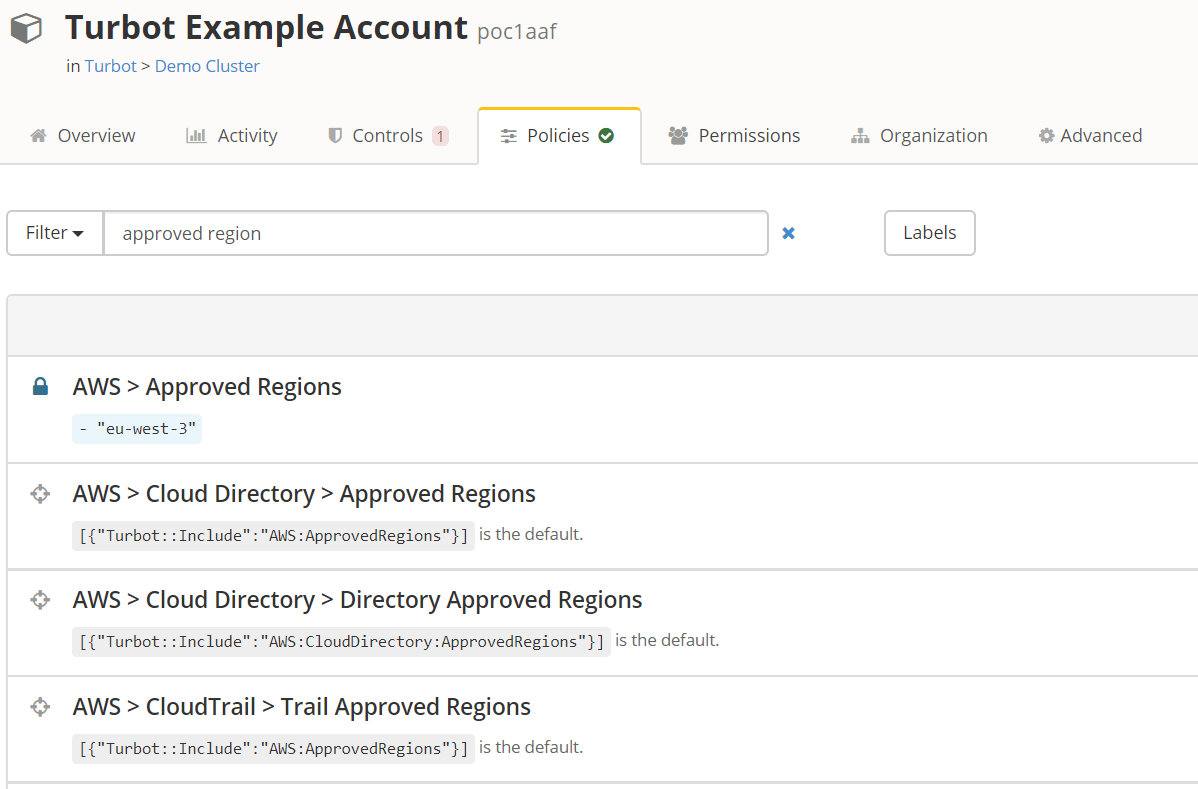
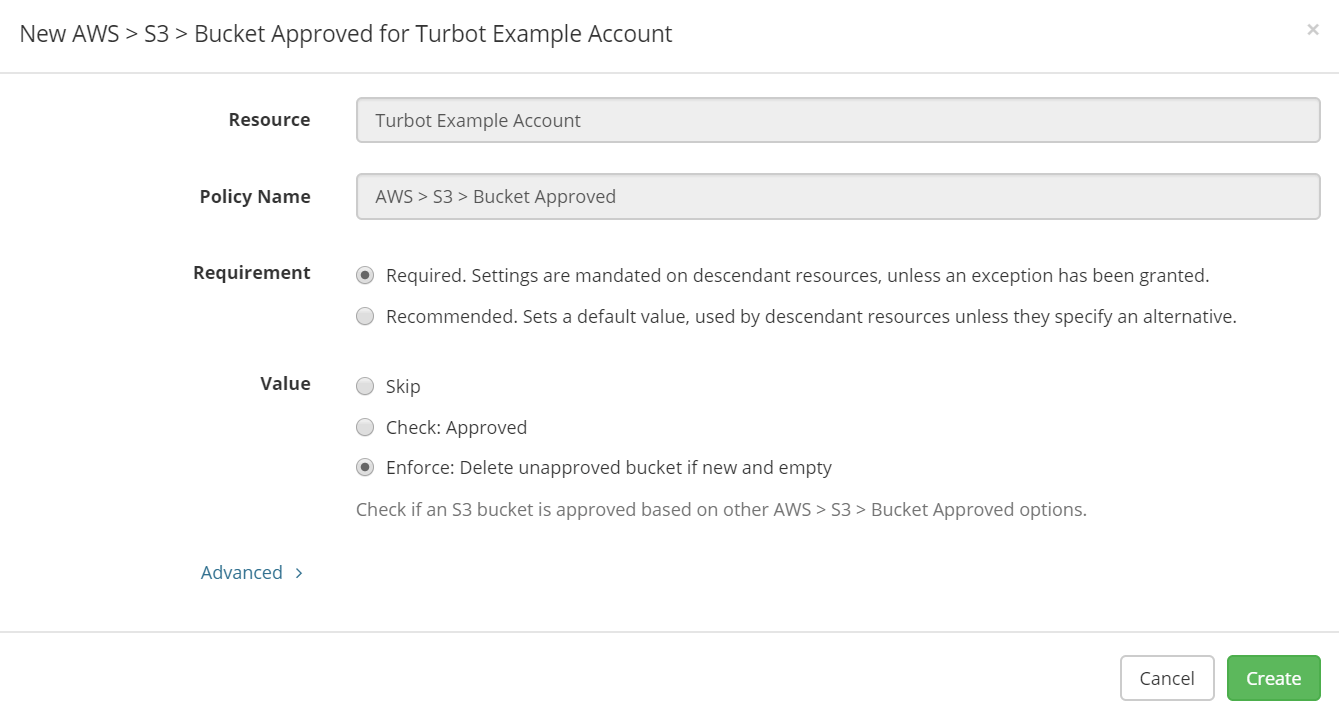
As an example, if a privileged user creates an S3 bucket in an unapproved region, Turbot Guardrails will detect it and delete the bucket within seconds. In Turbot Guardrails you can set varying policies for regional enforcements across a multi-account model across various AWS services.
For Data Protection:
From an identity perspective, Turbot Guardrails has a robust identity engine that allows customers to define permanent or time-based rights per user from AD/SAML per AWS services across a multi-account AWS model (along with OS, DB, Turbot Guardrails and SaaS tools).
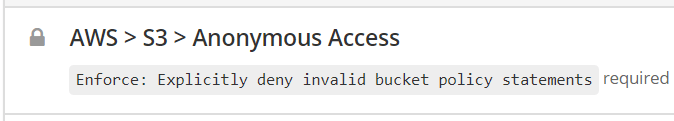
From a routing/networking perspective, Turbot Guardrails has 100s of guardrails to ensure boundary protection on various PaaS resources (cross-account, anonymous, CIDR restrictions, etc.) and VPC services such as EC2, RDS, RS, etc. Turbot Guardrails can remediate misconfigured routing configurations, security group rules, DNS records, NACLs, and other networking constructs.
Contact us for more information about compliance guardrails, or schedule a demo to see how Turbot Guardrails can enhance and support your cloud team's compliance efforts.
