Many of our enterprise customers use Turbot guardrails to ensure continuous compliance of their cloud infrastructure with specific industry standards such as NIST 800-53 and CIS.
Beyond our Financial Services customers, many organizations need the ability to provide PCI compliance to protect cardholder data. Turbot Guardrails reduces the effort required to comply with PCI regulations and enforces policies to protect Payment Card Information (PCI). It's not enough to just be PCI compliant at audit time; Turbot Guardrails helps to ensure continuous compliance with real-time corrective actions any time to eliminate configuration drift. The enterprise can ensure that DevOps teams use only PCI-eligible services, and that they securely process, transmit and store PCI data by utilizing the following guardrails:
1. Whitelist only PCI-eligible Services
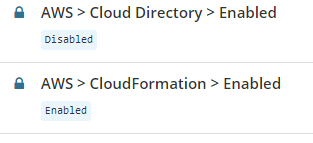
Using Turbot Guardrails, customers can whitelist only PCI-eligible AWS, Azure, and GCP Services, AMIs, RDS Engine Types, etc. All other services can be disabled to ensure that non-PCI compliant services are prevented from being used. The full list of eligible services is available for AWS, as part of the AoC for Azure, and GCP.
2. Enforce Encryption Standards
Turbot Guardrails offers Encryption at Rest and Encryption in Transit guardrails that can be enforced across various PCI-eligible services.
4. Track and Monitor All Access to Network Resources and Cardholder Data
Turbot Guardrails provides full transparency to all AWS, Azure, GCP, and Turbot Guardrails configurations and events. Turbot Guardrails Central Log Management capabilities aggregate AWS, Azure, GCP, and Turbot Guardrails activity logs to regional logging buckets per account. Users can view log details through raw logs located in S3. Using the Turbot Guardrails console, they can also view current and prior event history per various levels of the resource hierarchy.
5. Do Not Use Vendor-Supplied Defaults for System Passwords and Other Security Parameters
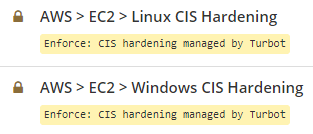
Turbot Guardrails automates security hardening of Operating Systems to CIS Benchmarks, enforcing hundreds of security settings within Windows and Linux. Turbot Guardrails can perform user, group, and SSH key management, can restrict access key creation, and enforce rotation of access keys.
6. Identify and Authenticate Access to System Components
Turbot Guardrails can connect to your organization's Active Directory, LDAP, or SAML provider, and federate users across your cloud providers. The controls of these directory services (invalid login attempts, minimum lockout durations, idle session timeouts) are then extended and applied to environments where Turbot Guardrails is managing permissions. Turbot Guardrails can also enforce account expiration, and enforce activity timers. Turbot Guardrails also performs user, group, and SSH key management within guest Operating Systems, and can perform user, group, and password management within databases. Turbot Guardrails also offers support for Multi-Factor Authentication.
7. Develop and Maintain Secure Systems and Applications
Turbot Guardrails can ensure that patching is up to date within instances running in your cloud environment. Turbot Guardrails can enforce specific AMIs or Publishers in AWS ensuring that only selected, hardened AMIs are utilized. Turbot Guardrails also integrates with your CI/CD pipeline, and can automate application deployment ensuring that the latest approved versions of custom applications have been deployed.
8. Install and Maintain a Firewall Configuration to Protect Cardholder Data
VPCs, security groups, ACLs, and other networking controls can support the firewall and network segmentation requirements of PCI compliance. Turbot Guardrails can automate networking controls, control security group configuration, implement access restrictions, and enforce approved utilization of networking components.
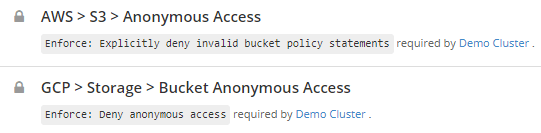
Turbot Guardrails can also ensure that networking components are configured correctly, in accordance with your policies, to prevent inadvertent exposure of data, and can provide protection of data from being exposed with anonymous access. Turbot Guardrails routing guardrails enforce that resources only live in approved boundaries (e.g. Public, Intranet, Private in VPC).

9. Whitelist Regions
Turbot Guardrails can ensure that only PCI certified regions are utilized for data storage and data processing. By configuring the "Approved Regions" Policies, Turbot Guardrails can ensure that data is only placed in PCI compliant regions / cloud provider data centers that have been PCI certified. Turbot Guardrails allows you to configure approved regions for individual services, and can include different approved regions for each service.
10. Regularly Test Security Systems and Processes
In any computing environment, the risk is rarely in the platform. The risk is what people do with the platform. It is not enough to ensure point-in-time compliance during deployments. Over time application and infrastructure configurations drift causing inadvertent data exposure. Ensuring continuous compliance, security, and operational best practices will maintain adherence to control measures. Turbot Guardrails Software Defined Operations help to ensure continuous compliance with your organization's defined policies. With Turbot guardrails (preventive controls, detective controls, real-time automated corrective actions, and recurring environment scans), Turbot Guardrails can ensure consistency and compliance with your policies, and can be utilized to demonstrate continuous compliance to auditors.
Contact us for more information about compliance guardrails and a full demo of how Turbot Guardrails can enhance and support your cloud team.