Turbot Guardrails now supports user managed AWS access keys, allowing users to create, rotate, and delete access keys from the Turbot Guardrails console for each of their accounts. Access keys were previously only available for service users, adding overhead when needing to use the AWS CLI and other tools that leveraged access keys.
Managing Access Keys
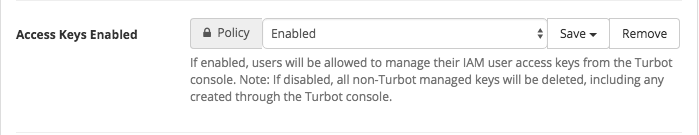
Before users can begin creating access keys from the Turbot Guardrails console, the "Turbot > AWS Users > Access Keys Enabled" option will need to be Enabled:
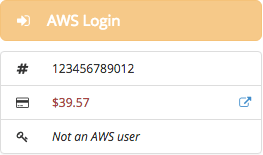
The user will need to have an IAM user in the account, else the create option will be disabled (the AWS login button is also disabled):
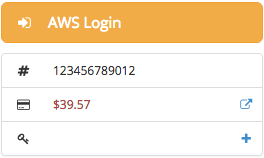
To create a key, click Create (+):
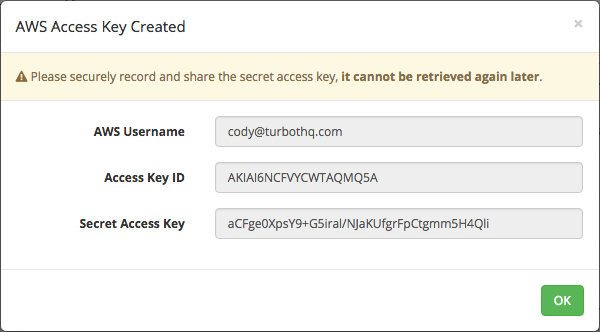
A modal will appear with the AWS username, access key ID, and secret access key:
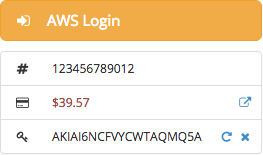
After a key has been created, the access key ID will be displayed, along with the options to rotate or delete the key:
Expiring Access Keys
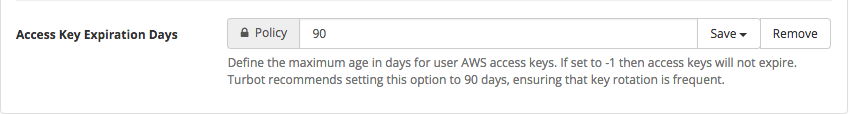
Access keys can also be set to expire through the "Turbot > AWS Users > Access Key Expiration Days" option:
Expired keys will be struck-through on the Turbot Guardrails console and automatically be deactivated to prevent further use:
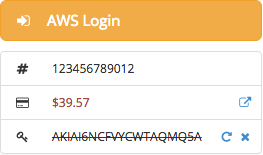
Turbot Guardrails recommends setting a short expiration period to enforce frequent rotations as a security best practice.
